Overview
A Provenance Mark is a forward-commitment hash chain to establish cryptographic sequential ordering for linked digital objects. Each mark in the chain commits to preceding and subsequent content, preventing retroactive insertion or modification without requiring timestamps or trusted witnesses. This enables tracking of editions, state changes, and histories for controller documents, credentials, and evolving structures.
Why are Provenance Marks Important?
In an age of rampant AI-powered manipulation and plagiarism, determining provenance is more important than ever. Provenance Marks ensure public and easy verification of provenance, offering robust security and intuitive usability. Provenance Marks are particularly valuable for securing artistic, intellectual, and commercial works against fraud and deep fakes, protecting creators’ reputations and the integrity of their creations.
How Do Provenance Marks Work?
Each Provenance Mark is a collection of structured binary date that contains 5-6 data elements. A linked set of Provenance marks together form a chain of provenance, which proves that a set of objects are linked (and in what order).
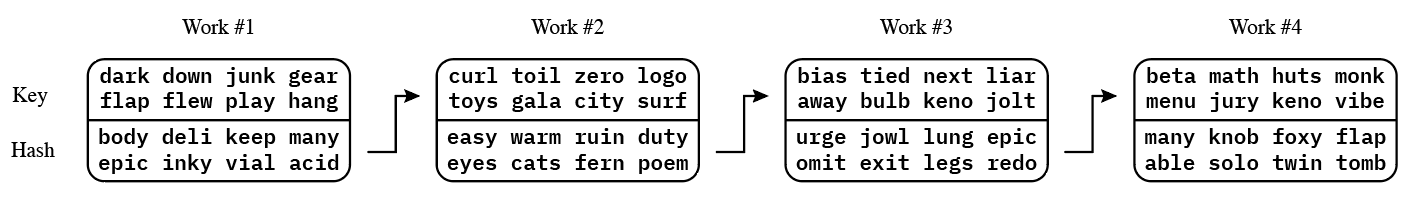
The elements in a Provenance Mark are:
- key. A random number, generated from a seed for the chain of provenance.
- hash. A SHA-256 hash that commits to the next key in the chain.
- id. The unique identifier for a chain of provenance, which is the
keyof the genesis mark. - seq. The sequence number for the Provenance Mark in the chain, starting from
0for the genesis mark and incrementing from there. - date. The date of the Provenance Mark’s creation.
- info (optional). CBOR metadata for the mark.
It’s the hash that actually creates the chain because it commits to the content of the next Provenance Mark in the chain. (In fact, it commits to everything in the next Provenance Mark in the chain, but the next key is the random element that couldn’t otherwise be known.)
hash=trunc(H(key||nextKey||id||seq||date||info),linkLen)
Provenance Marks come in four resolutions (sizes): low, medium, quartile, and high. They vary in size from 16 bytes (low) to 106 bytes (high), and the precise construction of the various fields depends on the size, as described in BCR-2025-001.
Provenance Marks are often represented as Bytewords, which allows their simple & clear depiction using a number of simple words. A low-resolution mark, consisting of 16 bytes + 4 bytes of checksum, might be represented as follows:
taco kite buzz nail arch
fact bias nail apex plus
deli wave cats webs ruin
legs quiz draw work onyx
How to Get Started with Provenance Marks

- Read BCR-2025-001: Provenance Marks: An Innovative Approach for Authenticity Verification
- Choose a chain (either a sequence of objects or an object that changes over time) to mark with a chain of provenance
- Test Provenance Marks with the Provenance Mark CLI.
- Use the rust or swift library to implement Provenance Marks.
Videos
|
June 2025 Meeting (Provenance Marks):
|
Libraries
Provenance Marks Libraries
| Language | Repo | Contributor | Status |
|---|---|---|---|
| Rust | provenance-mark-rust | Blockchain Commons | |
| Swift | Provenance | Blockchain Commons | |
| TypeScript | provenance-mark | Leonardo Custodio |
Links
Intro:
*BCR-2025-001: Provenance Marks: An Innovative Approach for Authenticity Verification
Developer Reference Apps: